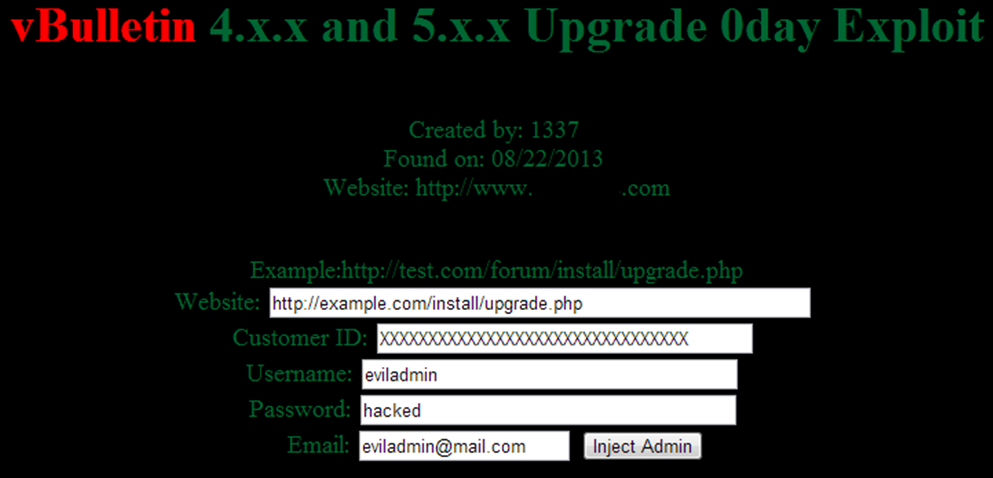
vBulletin Exploit - Perhaps yet another reason why security should not be left in the hands of the "end user?"
You probably already heard/read about attacks compromising websites using a "security weakness in sites powered by the forum vBulletin." In case you missed it, there's a really good post about this on Brian Krebs' website.
This wouldn't be the first attack targeting a vulnerability in vBulletin, or any other CMS for that matter; however, the peculiar thing about this for me was in the vulnerability itself. According to Krebs, the vulnerability results from a security weakness that is exposed when users fail to remove the “/install” and “/core/install” directories on sites running 4.x and 5.x versions of vBulletin.
How often do we see software vendors instructing that installation files and/or folders be removed after installing/upgrading software or components. In fact, many 'self-installable' applications (both open source and commercial) out there typically come with a similar set of 'post-installation' instructions. Here's one from Kimai:
Remove the “install” directory after the installation!After you removed the “install” directory you may login into Kimai using the following credentials:
And yet another from Prestashop:
"An easy way to improve your installation's security is to delete some key files and folders. This is done using your FTP client, directly on the server."Items to delete:
- The "install" folder (imperative).
- The "docs" folder (optional).
- The "README.md" file (optional).
Admittedly, I've personally never encountered a proof of concept that exploits a vulnerability related to the install directory (at least before this one, anyway), but it stands to reason that such warnings are given in light of the security implications of leaving the installation scripts/folders on the server after the installation of such software is complete. It also stands to reason that the creators of such software are well aware of potentially exploitable vulnerabilities related to these directories.
A major downside to this approach (i.e. requiring that users delete potentially vulnerable installation files/folders from their account) is that not all users are security "aware;" and even with those who are, security awareness is somewhat hierarchized -- so to speak -- as different users have different levels of security consciousness. Considering the spate of self-proclaimed Webmasters today, coupled with this fluctuating nature of user security awareness, it's even more imperative for software vendors to take a different approach to this.
If Imperva's security advisory is anything to go by, this particular exploit is a good example why it is a bad idea to leave security in the 'hands' of the end-user, as end users are notoriously lacking in security best practices.
So far, nearly 35,000 sites have reportedly been hacked as a result of this vulnerability. Rather than require users to delete potentially vulnerable installation files, perhaps creators of software that target a variety of end users might want to consider enforcing this directive, instead.
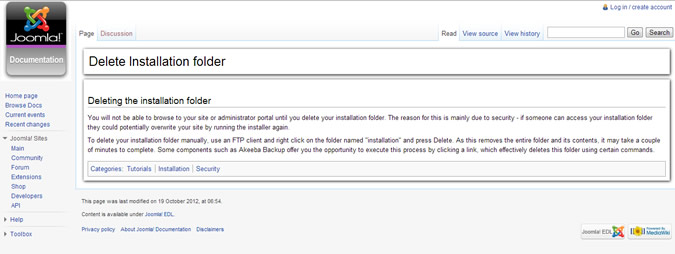
Joomla and a few others seem to have the right idea -- in a typical Joomla install, you will not be able to browse to your site or administrator portal until you delete the installation folder:
As far as security goes, it isn't simply enough to expect that users will adhere to security policies and/or best practices. Steps must be taken to enforce security measures. The way I see it, the same principle should apply to software vendors; software creators and programmers owe it a responsibility to the end user to ensure that -- to the best of their ability -- the software they release is free from defects and/or vulnerabilities that could ultimately compromise the security of the end-users' systems, and potentially result in loss.
Comments
Mantenere l'eccellente lavoro!
</a>
web hosting forum for the industry professionals and enthusiasts,
discussing general hosting, reseller opportunities, VPS and dedicated
solutions